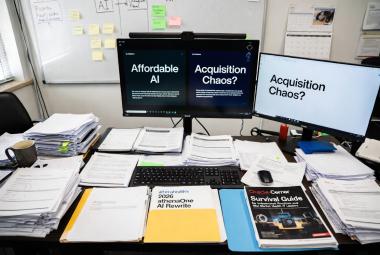
From Interlock's 2.7M PHI Strike to Paper Charts at 35 Clinics: A 2025-2026 Ransomware Playbook and Downtime Survival Guide for Healthcare IT

I. When the Screen Goes Dark
Consider two scenarios that played out in real healthcare facilities in 2025 and 2026.
In April 2025, a kidney dialysis patient in the United States showed up for a routine treatment session. The staff could still see her. But access to her lab history, her medication thresholds, and her individualized dialysis parameters -- all of that was locked inside a database that an Interlock ransomware operator had encrypted six days earlier. The organization -- DaVita, one of the largest kidney care providers in the country -- had activated manual protocols and patient care continued. But the records for 2.69 million patients had already been copied and were sitting on a dark web leak site.
In February 2026, a patient arrived at a University of Mississippi Medical Center clinic for a follow-up appointment. There was a sign on the door: the clinic was closed. So were the other 34-plus statewide clinic locations. Epic was offline. Phones were down. Email was down. Scheduling was down. Nurses at the inpatient facilities were writing orders by hand. The outage lasted nine days.
These two incidents -- separated by ten months and involving different organizations -- tell the same story. The Interlock ransomware group has developed a documented playbook for attacking healthcare infrastructure that is sophisticated, financially motivated, and actively evolving. And the operational reality of what happens when an EHR goes dark is no longer theoretical. We have two detailed case studies to learn from.
This article synthesizes both into a single resource for healthcare IT directors, HIPAA compliance officers, and executives at small and critical access hospitals who need to understand the threat and pressure-test their contingency plans.
II. Executive Timeline: Interlock's Healthcare Targets
Interlock emerged as a ransomware-as-a-service (RaaS) operation in September 2024. By mid-2025, it had become one of the most prolific threat actors specifically targeting healthcare. In July 2025, FBI, CISA, and HHS issued a joint advisory warning organizations about Interlock's tactics, techniques, and procedures. The following table maps the confirmed major incidents.
| Date | Target | PHI / Data Stolen | Operational Impact | Status |
| Apr 2025 | DaVita (dialysis) | 2.69M individuals; SSNs, dialysis records, lab results | Partial outage; patient care continued; billing disrupted; $13.5M costs | No ransom paid; data leaked; class actions filed |
| May 2025 | Kettering Health (OH) | 941 GB / 732,000 files; ID cards, financials, PHI, pharmacy records | System-wide outage; 600 apps down; ambulance diversions; Epic offline 13 days | No ransom paid; data leaked; 200+ lawsuits filed |
| Jul-Aug 2025 | City of St. Paul, MN | 43 GB; passports, employee records, public health budgets | City networks offline; paper processes; National Guard/FBI engaged | No ransom paid; data published |
| Feb 2026 | UMMC (Feb 19 - Mar 2) | Under review; PHI breach notification pending | 35+ clinics closed 9 days; Epic/phones/email offline; pen-and-paper protocols | Clinics reopened Mar 2; federal partners engaged; breach determination pending |
| IMPORTANT -- UMMC ATTRIBUTION NOTE: As of March 23, 2026, UMMC has NOT publicly attributed the February 2026 incident to Interlock, and has NOT confirmed a final PHI breach count. UMMC is included in this article because its documented operational response -- nine-day clinic closure, paper protocol activation, federal partner engagement -- is a direct, real-world example of HIPAA contingency planning under 45 C.F.R. Sec. 164.308(a)(7). Do not treat the proximity of UMMC in this table as confirmation of Interlock involvement. The threat actor behind the UMMC attack has not been publicly named as of publication date. |
III. Interlock's Tactics, Techniques, and Procedures
Understanding how Interlock operates is not an academic exercise. The attack chain is consistent enough across DaVita, Kettering, and other confirmed victims that it functions as a fingerprint -- and a defensive checklist.
The ClickFix Entry Point
Traditional ransomware entry via phishing email is well understood and at least partially mitigated by modern email security tools. Interlock's preferred initial access technique is different and more insidious. ClickFix delivers a fake browser notification -- typically a 'fix required' or 'update needed' prompt that appears on a compromised but otherwise legitimate website. When the victim clicks through, they unknowingly execute a PowerShell command that establishes Interlock's foothold.
This matters for healthcare specifically because clinical staff interact with external websites constantly -- vendor portals, insurance platforms, reference tools, continuing education sites. The prompt looks like a routine browser maintenance message. No email attachment. No suspicious sender. Standard email security controls do not catch it.
Persistence and Dwell Time
Once inside, Interlock does not immediately detonate. Forensic analysis of the DaVita attack confirmed the initial breach occurred March 24, 2025 -- nineteen days before encryption was detected on April 12. IBM X-Force researchers analyzing a related Interlock campaign identified a PowerShell-based C2 client called Slopoly, a backdoor with strong indicators of AI-assisted development including unusually structured code, detailed inline comments, and systematic error handling that human malware authors rarely produce.
The dwell time is deliberate. Interlock uses it to map the target environment, identify the most valuable data repositories (lab databases, financial records, identity documents), and stage the exfiltration before encryption begins. By the time the organization detects the attack, the data is already gone.
Double Extortion: Encrypt and Steal
Every confirmed Interlock attack on a healthcare organization has used the same extortion model: encrypt files to disrupt operations and pressure payment, while simultaneously threatening to publish stolen data on the dark web if the ransom is not paid. DaVita, Kettering Health, and St. Paul all declined to pay. In each case, Interlock published the stolen data.
The 72-hour negotiation window Interlock provides is a calculated pressure tactic. Healthcare organizations that cannot restore operations quickly face care disruption, potential patient harm, and board-level scrutiny -- all of which increase the likelihood of payment. The Kettering ransom note, viewed by CNN, was direct: pay or the data goes public.
The TTP breakdown below maps each phase of the attack chain to its specific healthcare risk. Use it as an input to your next security risk analysis under HIPAA Sec. 164.308(a)(1).
| Attack Phase | Interlock Tactic | Healthcare-Specific Risk |
| Initial Access | ClickFix: fake browser 'fix' prompt delivered via compromised legitimate websites; victim runs PowerShell without realizing it | Clinical staff clicking routine-looking browser prompts; no specialized technical knowledge required from attacker |
| Persistence | PowerShell C2 client; AI-assisted custom malware (Slopoly); NodeSnake and InterlockRAT backdoors maintained for weeks before detonation | Dwell time averages days to weeks -- long enough to map EHR structure and lab database schemas before encryption |
| Exfiltration | Rclone utility used to exfiltrate over encrypted channels; data staged before encryption for double-extortion leverage | Lab databases (DaVita), file servers (Kettering), municipal PHI-adjacent systems (St. Paul) all targeted specifically |
| Encryption | JunkFiction loader; SYSTEM-level scheduled task; Windows Restart Manager unlocks files before encryption; extensions: .!NT3RLOCK or .int3R1Ock | Encrypts EHR, scheduling, phones simultaneously -- maximizes operational disruption to force payment |
| Extortion | 72-hour negotiation window; dark web leak site; data published in stages when ransom not paid; secondary scam calls to patients | Kettering patients received scam payment calls within hours of outage; compounds reputational and regulatory exposure |
The AI Malware Development Signal
The IBM X-Force identification of AI-assisted malware development in the Interlock campaign deserves specific attention. The Slopoly backdoor showed structural characteristics -- systematic error handling, organized code comments, consistent formatting -- that are atypical of human-written malware. This is not a theoretical concern about future threats. It is a documented capability in an active campaign that targeted healthcare organizations in 2025.
The practical implication is that signature-based detection has a shorter shelf life against AI-assisted tools. Interlock can generate novel malware variants faster than threat intelligence can be distributed. Behavioral detection -- looking for the PowerShell patterns, the Rclone exfiltration activity, the scheduled task execution -- is more durable than relying on known file signatures.
IV. What EHR Downtime Actually Looks Like: UMMC February 2026
Day One: February 19, 2026
Early on the morning of February 19, University of Mississippi Medical Center detected a cybersecurity incident. Within hours, the scope was clear: Epic, the organization's primary EHR platform, was offline. So were phones, email, and scheduling systems. The decision was made to close all statewide outpatient clinic locations -- more than 35 sites -- and shift inpatient and emergency operations to manual downtime procedures.
That last phrase -- 'manual downtime procedures' -- is the HIPAA contingency planning requirement made real. For the nine days that followed, clinical staff at UMMC's inpatient facilities did what those procedures require: paper-based charting for patient assessments, handwritten medication orders, manual vital-sign documentation, verbal handoffs at shift changes. Dialysis continued at one site. Emergency services remained available.
| KEY FIGURE: Nine days -- the duration of UMMC's clinic closure. Kettering Health's comparable outage lasted thirteen days before core Epic components were restored. Does your contingency plan document a realistic recovery timeline, and has it been tested? |
The Paper Protocol Reality
Both UMMC and Kettering Health executed what HIPAA calls the 'Emergency Mode Operation Plan' under Sec. 164.308(a)(7)(ii)(C) -- the requirement that covered entities maintain operations while in emergency mode. In practice, this meant:
Pre-printed paper forms for clinical orders, medication administration records, and assessment documentation
Manual patient ID verification procedures at care transition points where electronic records were unavailable
Pharmacy staff reverting to paper-based medication reconciliation and dispensing logs
Lab staff maintaining manual requisition and result-reporting workflows
Nursing staff managing paper-based vital sign tracking on bedside documents rather than EHR flowsheets
These are not improvised responses. They are tested procedures that organizations are required to have under the HIPAA contingency planning standard. The UMMC and Kettering incidents validate that the standard exists for exactly this reason -- and expose what happens when those procedures have not been practiced recently.
Communication Collapse and Secondary Risks
One underappreciated dimension of both incidents was the communication layer failure. When Epic goes offline, the phones and call centers often go with it. Kettering Health's call center went offline simultaneously with its clinical systems. Within hours, patients began receiving scam calls from individuals impersonating Kettering staff and requesting credit card payments for medical expenses. Kettering had to suspend all outbound billing calls as a precautionary measure.
UMMC faced a similar challenge with patient notifications. The organization relied on a third-party vendor for outreach communications, and that dependency created days of delay in reaching patients with scheduling updates. The vendor relationship -- and its associated business associate agreement -- becomes a critical path item during an incident, not just a compliance checkbox.
The Backlog Problem
Kettering Health reopened for key services on June 11-13, 2025 -- more than three weeks after the initial attack. Even after normal operations resumed, staff faced the task of entering all paper-documented patient encounters into Epic retroactively. Every handwritten order, assessment, and medication administration record needed to be transcribed into the EHR to maintain accurate patient histories.
UMMC's clinic reopening on March 2 with extended hours addressed the patient volume backlog, but the medical record reconciliation problem persists regardless. For compliance officers, this creates a documentation integrity question: are the paper records being transcribed accurately, completely, and within the timeframes required for their specific patient populations?
V. HIPAA Compliance Matrix: What These Incidents Trigger
The following table maps each operational element of the UMMC and Kettering responses to the specific HIPAA Security Rule provisions they implicate. It is designed to function as a gap analysis starting point for compliance teams.
| Downtime Requirement | What UMMC / Kettering Actually Did | HIPAA Reg Reference |
| Paper-based clinical documentation | Pre-printed downtime forms for orders, vitals, medication administration; nurses reverted to manual charting within hours of outage | Sec. 164.308(a)(7) -- Contingency Plan: Data Backup + Emergency Mode |
| Critical care continuity (ER / dialysis) | UMMC kept ER and inpatient open; one dialysis site stayed operational; Kettering ERs open with ambulance diversions at start | Sec. 164.308(a)(7)(ii)(C) -- Emergency Mode Operation Plan |
| Communication alternatives | Kettering suspended all phone-based billing; UMMC used third-party vendor for patient notices; call centers went offline for days | Sec. 164.310(b) -- Workstation Use; Sec. 164.530(b) Workforce Training |
| Scheduled procedure triage | Procedures evaluated case-by-case on patient safety criteria; elective cases rescheduled across extended hours post-reopening | Sec. 164.308(a)(7)(ii)(D) -- Testing & Revision Procedures |
| System restoration sequencing | Kettering restored core Epic components June 2 (13 days post-attack); full normal operations June 11-13; UMMC reopened clinics Mar 2 (9 days) | Sec. 164.308(a)(7)(ii)(B) -- Disaster Recovery Plan |
| Law enforcement + federal notification | Both organizations engaged FBI, CISA; Kettering confirmed eradication of all Interlock tools before declaring restored operations | Sec. 164.308(a)(6) -- Security Incident Procedures |
Two compliance obligations warrant specific emphasis beyond the table.
Breach Notification (Sec. 164.404-414): DaVita's response timeline is the documented standard in this wave of incidents: OCR breach portal filing, individual notification letters, and complimentary credit monitoring offers for affected patients. UMMC has not yet confirmed the scope of PHI exposure from its February incident; the 60-day individual notification clock runs from the date the breach is confirmed, not discovered. If your organization experienced unauthorized access to ePHI at any point during an outage, the obligation exists regardless of whether the attack was ultimately contained.
Contingency Plan Testing (Sec. 164.308(a)(7)(ii)(D)): The regulation requires that covered entities periodically test and revise contingency plans. 'Periodically' has no defined frequency -- which means it is frequently underdocumented and rarely tested at full scale. UMMC and Kettering both had downtime procedures; both experienced significant operational disruption despite having them. The question for your organization is not whether you have a contingency plan document. It is whether your clinical staff has executed it under simulated conditions within the last 12 months.
VI. Risk Mitigation Roadmap
The following checklist is built directly from the documented failure points in the DaVita, Kettering, and UMMC incidents. Each item maps to a specific attack vector or recovery gap -- not a generic best-practices list.
| Action Item | How to Execute | Priority |
| Load Interlock IoCs from CISA/FBI/HHS July 2025 alert | Search SIEM for ClickFix PowerShell patterns, Rclone activity, .!NT3RLOCK file extensions, JunkFiction loader signatures | IMMEDIATE |
| Audit lab and vendor databases for unnecessary external access | DaVita's dialysis labs database was the entry point; isolate similar systems behind separate network segments with deny-by-default rules | IMMEDIATE |
| Deploy and enforce MFA on all remote access and VPN entry points | ClickFix exploits credential reuse after initial access; MFA breaks the lateral movement chain at the network perimeter | HIGH |
| Conduct a live EHR downtime drill (full paper protocol) | Simulate 24-to-48-hour Epic outage; require paper charting, manual orders, and verbal handoffs; validate that all clinical staff know where downtime forms are stored | HIGH |
| Verify offline backup integrity and restoration timelines | Kettering took 13 days to restore core Epic; UMMC 9 days for clinics -- test whether your RTO matches your documented contingency plan | HIGH |
| Review BAAs with all lab, analytics, and third-party platform vendors | DaVita's labs database processed records for third-party providers; each downstream vendor relationship is a potential exfiltration vector | MEDIUM |
| Establish a documented no-ransom policy and align cyber insurance coverage | Confirm your policy covers: breach notification costs, credit monitoring, business interruption, and class action defense -- all triggered in DaVita and Kettering cases | MEDIUM |
| Train clinical staff on ClickFix and social engineering vectors annually | ClickFix targets browser-level interactions that clinical staff consider routine; standard phishing training does not cover this vector -- update curriculum | ONGOING |
| CAH / RURAL HOSPITAL NOTE: If you are operating at a Critical Access Hospital with limited IT staff, the two highest-priority items on this list are the ClickFix workforce training update and the downtime drill. Both are low-cost, high-impact, and directly tied to the specific vectors Interlock has used against healthcare targets. The CISA IoC loading requires security tooling you may not have -- that is a vendor conversation, not a training problem. |
VII. Looking Ahead
AI-Enhanced Ransomware Is Not a Future Problem
The IBM X-Force identification of AI-assisted malware development in the Interlock campaign is a documented present-day capability, not a projected threat. As generative AI tools become more accessible, the barrier to creating novel, evasion-resistant malware drops. Healthcare organizations should assume that the attack tooling they face in 2026 and 2027 will be increasingly resistant to signature-based detection, and invest proportionally in behavioral monitoring and anomaly detection.
The Class Action Liability Trajectory
Kettering Health is currently defending more than 200 lawsuits stemming from the May 2025 attack. Plaintiffs are pursuing both a class action and individual personal injury mass torts -- arguing that care disruption caused direct patient harm through delayed diagnostics, interrupted prescriptions, and canceled procedures. DaVita faces similar class action exposure. This litigation pattern establishes a precedent that ransomware incidents do not merely create regulatory exposure -- they create direct liability for patient outcomes during the outage period.
The implication for compliance officers and executives is that downtime procedure documentation is no longer just a HIPAA checkbox. It is a litigation defense. The ability to demonstrate that your organization had tested, documented, and properly executed contingency plans during an outage may be the difference between a settlement and a judgment.
The Third-Party Vendor Risk Concentration
Both the DaVita dialysis labs database and the Kettering Health file server attack demonstrate that Interlock specifically targets data repositories that aggregate records from multiple organizations. DaVita's labs database processed records for providers beyond DaVita itself. The downstream exposure hit organizations that had no direct vulnerability but whose patient data was held by a compromised business associate. Vendor risk management and business associate agreement enforcement are not administrative overhead -- they are the mechanism by which your security posture extends to the weakest link in your supply chain.
VIII. Conclusion
The Interlock ransomware group has demonstrated a consistent, repeatable playbook against healthcare targets. ClickFix entry. Extended dwell time. Lab and financial database exfiltration. Encryption of EHR and communications infrastructure simultaneously. Double extortion with a 72-hour window. Data published when ransom is refused.
UMMC's nine-day clinic closure and Kettering Health's three-week recovery are not cautionary tales about organizations that failed to prepare. Both had contingency plans. Both had downtime procedures. Both continued to deliver emergency and critical care through the incident. What they illustrate is the gap between having a documented plan and having a tested one -- and the real operational, patient care, and legal consequences of that gap.
For healthcare IT directors and compliance officers, the actionable takeaway is direct: load the CISA IoCs from the July 2025 joint advisory, schedule a full EHR downtime drill before your next compliance review, audit your lab and vendor database access controls, and confirm your cyber insurance covers the full spectrum of costs that materialized in these cases. The threat is documented. The defense steps are known. The window to act before the next incident is the one you have right now.
| RESOURCES: CISA/FBI/HHS Interlock Advisory (July 2025): cisa.gov | OCR Breach Portal: hhs.gov/hipaa | Kettering Health incident FAQ: ketteringhealth.org | HIPAA Contingency Plan guidance: hhs.gov/hipaa/for-professionals/security | FBI IC3 Reporting: ic3.gov |
Published: March 23, 2026 | Audience: Healthcare IT Directors, HIPAA Compliance Officers, CAH/Rural Hospital Executives
This article is for informational purposes only and does not constitute legal advice. Consult qualified legal counsel and cybersecurity professionals regarding your organization's specific obligations and security posture. Incident details are based on publicly available statements, news reporting, and regulatory filings as of March 23, 2026.